Visual Basic DllFunctionCall
 Paolo Palumbo (Paolo) <Ppalumbo1979 Paolo Palumbo (Paolo) <Ppalumbo1979 gmail gmail com> com> |
Friday, August 31 2007 21:47.00 CDT |
Recently, static analysis of Visual Basic executables has been made easier by the release of a very nice IDC script by Reginald Wong. On top of its analysis, I decided to create a script to automatically handle DllFunctionCall.
DllFunctionCall is found in the implementation of the Visual Basic Declare statements, that are used to call Windows API functions in Visual Basic 5/6 programs.
For example, lots of VB malwares do use such mechanism to call Windows APIs. Lets consider a simpe autorun VB worm: we load it into IDA, run the script provided by Reginald Wong, and start analyzing it. Analyzing the code, we find several references to code of this kind:
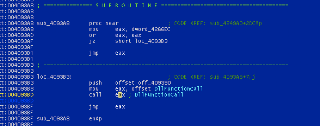
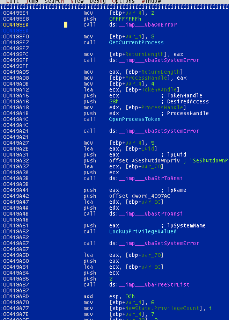
With a bit of manual intervention, the purpose of this code becomes clearer:

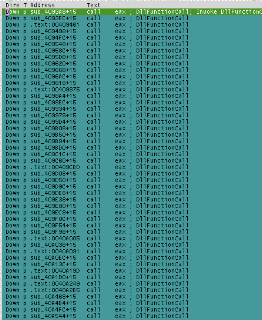
Analyzing this was easy. However, if we look at the number of calls to DllFunctionCall, we find that there are quite a lot of such calls, more than we do want to fix manually:
So I wrote a little script to handle this automatically: it will create functions where needed, will name functions properly and add type information. The previous list after running the script becomes:
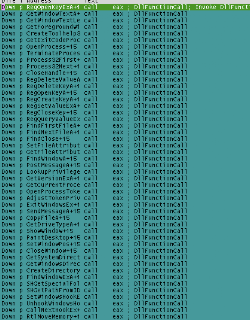
and:
Hopefully this will make your VB reversing sessions easier;) You can fetch the script here.